Cyber security is becoming an increasing concern for small business owners. Ranked as one of the leading causes of business failure in 2022, as cyber-attacks continue to become more prevalent, entrepreneurs must be prepared to tackle data breaches head-on.
From 2020-2021 alone, business-based cybersecurity breaches increased by 31%, according to a State of Cybersecurity Resilience report from Accenture. As the number of attacks per venture surged from 206 to 270 year on year, small businesses now fear the cash flow consequences of cybercrime.
In a post-pandemic landscape, where digitalisation demands are at an all-time high, the corporate shift online and the exponential growth of the e-commerce sector have only increased the chances of falling victim to cybercrime.
“Protecting critical infrastructure Industrial Control Systems, Operational Technology, and IT systems from cybersecurity threats is a difficult endeavour,” claims GovCon expert, Chuck Brooks. “Protecting such an enormous attack surface is no easy task, especially when there are so many varying types and security standards on the devices. It will only worsen in 2022 as connectivity grows.”
Read on as we navigate the cybersecurity landscape in 2022, and explore your own cyber hygiene in a data-dependent corporate sector. From blockchain security to remote working enhancements, find out how you can keep your business safe in a digital tomorrow.
Exploring The Cybersecurity Landscape In 2022
The cybersecurity landscape is nothing short of shocking in 2022. After global cybercrime grew by 600% on the back of the pandemic alone, there are still a number of cyber security trends hitting the headlines two years down the line.
As cyber hackers continue to target both consumer and company data, the overall cost of data breaching is expected to exceed $10.5 trillion in the next three years, according to Cisco.
Ransomware attacks remain the most prevalent in 2022 after they increased by 151% in 2021. Quickly followed up by IoT attacks and a rise in encrypted threats, it seems as if all forms of data breaches have risen in response to a global digital shift.
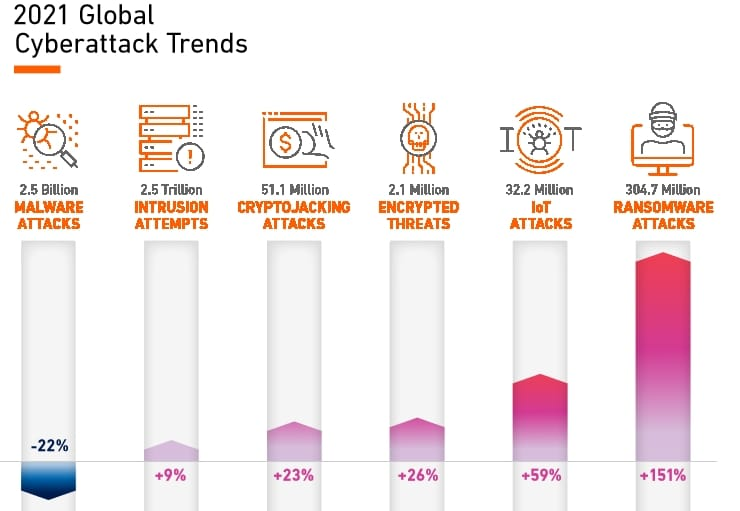
(Image Source: Compaitech)
Phishing also remains a leading threat as we step into Q3 of 2022, with over 90% of reported attacks originating as spear phishing emails. Spear phishing aims to target both individual and company social pages, using the data collected from a social platform to create a tailored email campaign that aims to encourage consumer engagement.
The growing popularity of cryptocurrency has also become a key target for smart data hackers. More consumers than ever before are sharing their financial data across fintech platforms. As a digitally active population completes cross-border transactions using a digital currency such as Bitcoin or Ethereum, they become susceptible to a number of new data breaches.
In fact, cryptojacking has risen by 23% as hackers learn new ways to mine cryptocurrency. Using a mix of malware installations and malicious code-jacking, defence systems are quickly breached, resulting in significant financial losses for the victim.
As we step into a post-pandemic landscape, all technology users are at risk of a data breach, especially business owners, sitting on a goldmine of consumer data, mobile and cloud-based systems.
“Most firms still do not know where all of the sensitive information is nor what the criticality is, and we continue to see breaches because of it,” states Securosis security analyst, Adrian Lane.
Let’s have a closer look at some of the key cybersecurity threats business leaders are up against in 2022 as we discover what the impacts of data breaching could mean for small business owners.
The Impacts Of Post-Covid Digitalisation
It’s no secret that Covid-19 accelerated the adoption of technology across the globe. As numerous lockdowns sent corporate workers inside and furlough schemes boomed, more consumers than ever before took to an online setting to keep in contact with both colleagues and loved ones.
In fact, as a result of lockdown conditions, digital activities increased tenfold. As social platforms such as TikTok took off among a Gen Z generation, 42% of the population claimed that they checked social media more frequently, and a further 27% saw their watch history lengthen on apps such as YouTube.
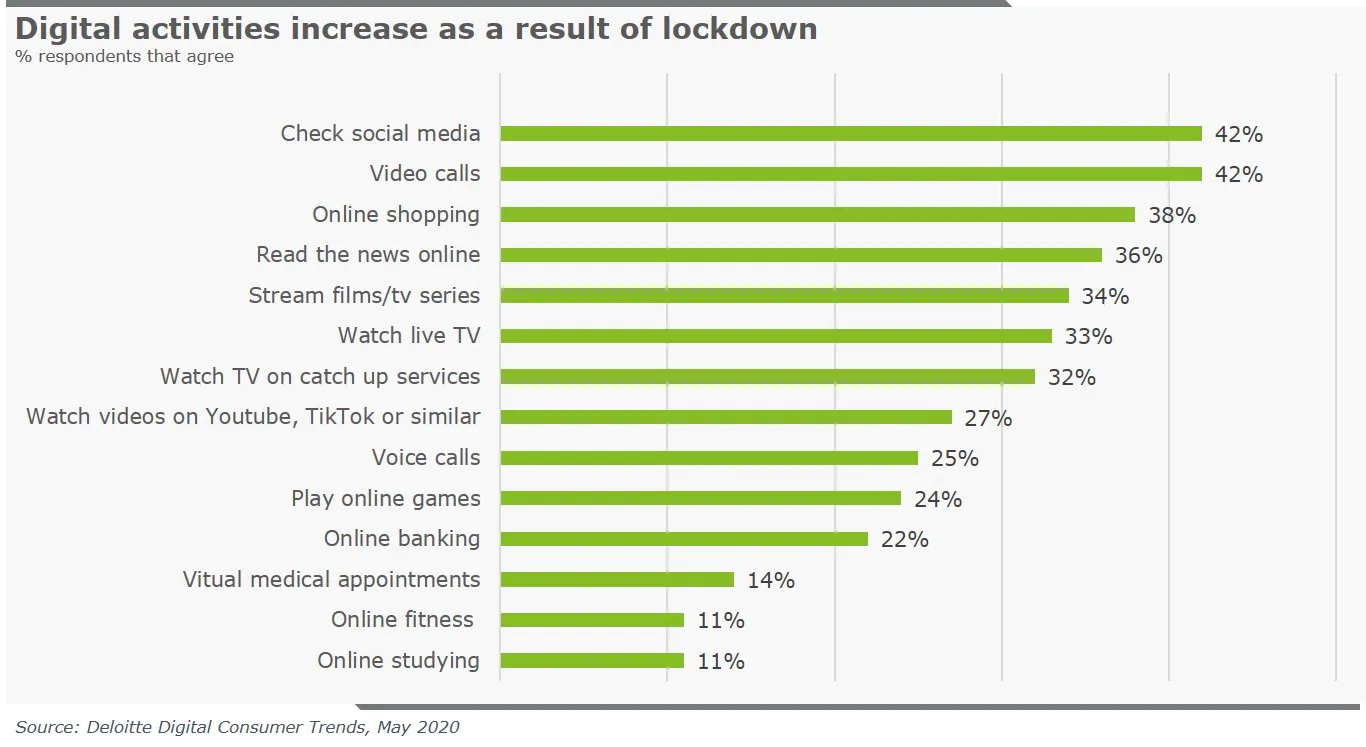
(Image Source: Deloitte)
While social media platforms saw the largest influx of user activity, a fifth of respondents in a Deloitte study claimed that they also used online banking more frequently as a result of the pandemic, with 60% revealing that they were now more likely to handle their finances online once restrictions were lifted.
Remote working trends also accelerated the adoption of a range of digital technologies. From immersive AR/VR aids that mimic the office, to the introduction of AI automation in a WFH setting, small business owners were some of the key campaigners for a digital shift.
However, while global-scale digitalisation had been tipped to revolutionise the corporate sector in the next decade, the rapid increase in technological adoption has not come with its drawbacks. In fact, over half of all small business owners were cornered by the possibility of cyber attacks in the wake of remote working trends.
With an increasing dependency on remote data sharing and third-party platforms, many WFH teams fear that a data breach is just a few steps away.
Are Small Businesses Prime Targets?
A 2021 report by Barracuda Networks found that small businesses were 350% more likely to be a victim of a cyber attack, than a larger enterprise. Without the same level of protection as industry giants, hackers are continuing to target CEOs and CFOs in rapidly expanding SMEs, in an attempt to harvest private financial data.
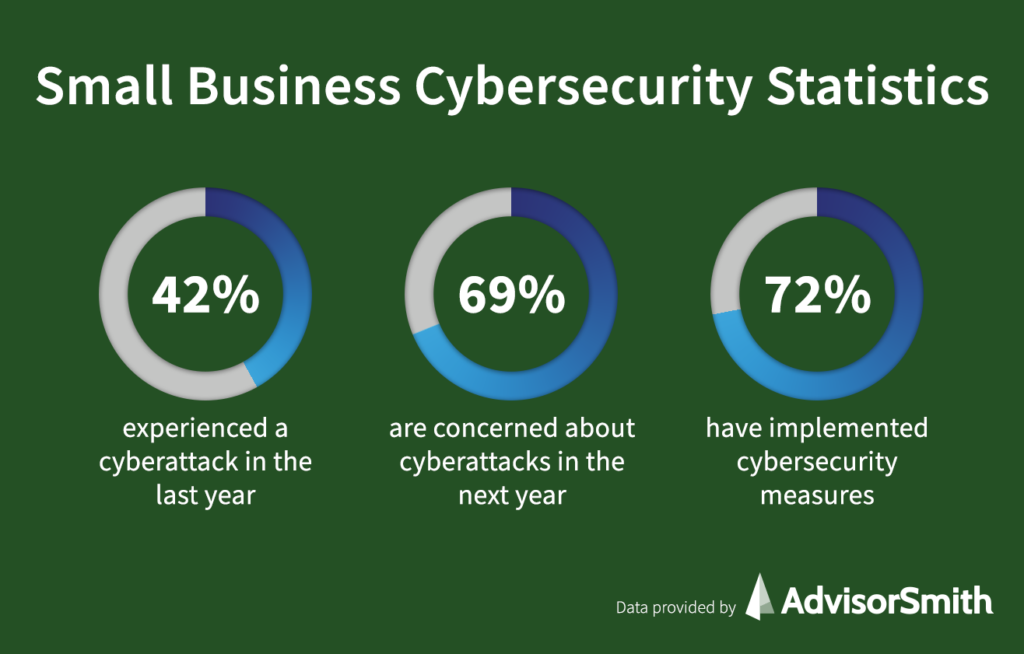
(Image Source: AdvisorSmith)
“Hackers target high-value accounts for takeover. Accounts of CEOs and CFOs are almost twice as likely to be taken over compared to average employees. Once they have access, cybercriminals use these high-value accounts to gather intelligence or launch attacks within an organization,” the report stated. “Executive assistants are also a popular target as they often have access to executive accounts and calendars and usually can send messages out on behalf of executive teams.”
As the startup scene continues to expand at an exponential rate, remote working trends have made smaller business ventures a key target for hackers. As employees adapt to digital communication platforms, human error is one of the leading causes of data breaching.
“The biggest risk companies will face in the coming year is the risk of having their data breached. Organisations for years have said, “it’s not if you’ll be breached, it’s when.” argues Kevin Coppins, Spirion CEO.
“The shift we are starting to see accelerate is organizations…experiencing multiple incidents in a single year, and the types of incidents are expanding. This is a direct result of the ever-expanding data universe, accelerated by the global pandemic and the evolving regulations surrounding sensitive data.”
The Top Cyber Threats To Look Out For
In a world where extensive data sharing has become the new norm, the number of cyber-based threats has risen in response. From a spike in social engineering to the risks of third-party exposure, here are some of the key hacking threats to be mindful of as you move forward.
Third-Party Hacking
As we step into 2022, third-party data hacking has become an increasing concern for both companies and consumers. In an e-commerce-dominated environment, where both business owners and their users are constantly sharing third-party data over a number of social, fintech and web-based platforms, the risk of a data breach becomes all the more real.
For remote ventures, in particular, an increasing trend to turn to the gig economy for freelance labour has heightened the risk of third-party data hacking. Turning to independent contractors, studies have shown that 96% of small business organisations grant external contracting systems access to a multitude of company data, putting them at risk of an attack.
Social Engineering
As 4.6 billion people engage with a social media platform daily, consumer-dominated sites such as Facebook, Instagram and Linkedin are constantly gathering third-party data surrounding consumer interactions, age, location and occupation.
In fact, in 2021 alone, hackers leveraged data from over 214 million Instagram, Facebook and Linkedin accounts, after breaching the well-known third-party platform contractor, Socialranks. With access to user information, smart hackers were able to craft phishing campaigns and commit an abundance of fraudulent activity.
Relying on human errors, rather than a technological breach, social engineering is becoming more popular in a social media-dominated landscape. In fact, a recent report from Verizon claimed that 85% of breaches are now attributed to human interaction.
Cloud Computing Risks
While the cloud is rated as one of the most secure data handling systems, its vulnerabilities are constantly being exposed by a new generation of smart hackers. With a data vulnerability score that has increased by 150% since the onset of the pandemic, experts at IBM suggest that web app breaches could be the leading cause of the cloud’s downfall.
However, as we step into 2022, we’re likely to see widespread adoption of cloud security’s new Zero Trust system update. Zero Trust security aims to improve the verification process and reduce the penetration of unrecognised devices.
A Peak In Ransomeware Attacks
Ransomeware based breaches are not only one of the most common forms of cyber attack but the most expensive. After a 2021 Cybereason survey found that 66% of small business owners sustained significant capital losses as a result of a ransomware attack, it’s no surprise that it has become widely feared by the corporate sector.
As ransomware variants continue to spread and expand, the average loss in a ransomware breach has now hit $200,000 in 2022 as a pose to $5,000 in just 2018. As more small businesses move their data sharing platforms into an online realm, the introduction of Ransomware-as-a-Service has only made it easier for cyber criminals to execute data-based attacks on weak data security systems.
Do You Have Poor Cyber Hygiene?
As both startup entrepreneurs and SME leaders adopt a growing concern about the reality of cyber hacking, it’s time to take a look at your own business venture and review your own cyber hygiene.
Referring to how you handle your technology use and safeguard your vulnerable data, prioritising cyber hygiene has become the key to success for small business owners at risk of a breach.
Currently, statistics show that more than half of all small businesses are not cyber safe, with more than 30% operating within unprotected networks. Worse still, recent studies have shown that 60% of small business owners still rely on memory when managing passwords and only half of the company leaders invest in a two-factor authentication system for added protection.
As WFH trends sore, small business owners must be on top of their cyber hygiene if they want to stay safe in an online landscape. In order to keep company data secure, both employees and employers must continue to seek data protection training, especially when logging on to personal devices in a remote setting.
If you’re concerned about your own cyber hygiene, fear not. We have you covered. Read on as we divulge our best-kept cybersecurity secrets, and share our top tips on how to keep your business cyber safe in 2022.
6 Steps You Can Take To Keep Your Business Safe
There are a number of steps you can take to keep your small business safe from a cyber invasion. From taking an audit of your current cyber security system to investing in new forms of protective software, such as blockchain technology.
Staging data smart in an online age is the key to continued business success. As more startup ventures than ever before fall victim to costly data breaches, entrepreneurs must be forward-thinking and prepared to face more small business challenges in a data-driven landscape.
Take a look at our six cyber safety tips, that are guaranteed to make your business more secure in 2022.
Audit Your Cybersecurity System
One of the easiest steps you can take towards a cyber-safe future is a step back. Taking time to audit your current cybersecurity, can aid you in identifying vulnerabilities in your data security system.
Carrying out a cybersecurity audit consists of conducting a comprehensive review of your current infrastructure and can aid business owners in detecting possible threats, the occurrence of human error and penetrable weak links, that could be exploited by a hacker.
Some of the key areas your audit should cover involve, your data security, network security, operational practices and system strength. Covering all bases will leave you in the best position for forming a new cyber security strategy, and could even enhance future staff training. For remote-based ventures, in particular, it’s also important to review the security of collaborative platforms, and the risks associated with using personal devices.
Teach Your Team To Be Cyber Safe
Human error is one f the leading causes of a cyber breach. Therefore, in a business environment, both the employer and employees must be on top of their own data protection habits.
“The majority of online scams rely on some form of human error, as it is far easier to compromise a single user than a whole system,” claims Carl Wearn, Head of e-crime at Mimecast. “Threat actors know this well and are continuing to exploit the human factor by tailoring scams to target current events and the fears of their victims”
The key here is to implement cyber-based training into your business strategy. Appointing your IT or HR team as a direct port of call for cyber-based safety training and advice is a great way to start. From teaching your team to spot cybersecurity red flags to introducing multi-factor authentication in a remote environment, making your team more cyber-aware is a quick route to success in an online domain.
Another factor to consider when enforcing cybersafety amongst your employees is password protection. After a recent Specops Software study revealed that 51% of small business employees have a ‘weak password’, it’s time to start prioritising password protection, especially on a remote team’s personal devices.
Keep Your Software Up To Date
Another key factor you must consider is your software health. Keeping your systems up to date with the latest security enhancers will prevent hackers from exploiting weak links in your security system.
Your operating system, in particular, is the root of the functionality of your device. While most operating systems have built-in virus protection, cyber threats are constantly changing and evolving, meaning that your system needs to be transformed in line with them. If you are on top of your system updates, you have a much better chance of deterring cyber-criminals, trained to hack popular operating platforms such as the cloud.
The key here is to enable an automatic update strategy. For mobile devices, in particular, most operating systems give you the opportunity to select ‘automatic updates’, taking away the pressure of manually keeping your systems fresh, while automatically working to deter cyber-hackers.
Better still, keeping on top of software updates can also offer a number of benefits aside from improved security. Often paired with new features and improved system enhancements, keeping your tech updated is the key to keeping your computer fresh, fast and efficient, especially in a corporate sector that relies on technology for success.
Secure Your Networks
As accommodating as a free Wi-Fi network may seem, that coffee-shop work session may just be the factor that costs you your data security. Connecting to an unsecured Wi-Fi network can put a small business at significant risk of a cybersecurity invasion.
Instead, smart entrepreneurs should invest in a portable network hotspot, that can ensure that a Wi-Fi connection is both secure and hidden from potential hackers.
For larger SMEs, company leaders should also consider network segmentation when operating on a wireless network. The key here is to distance the staff-based network from a visitor (guest) alternative, in order to ensure secure data sharing within the team.
Invest In Blockchain
For small business ventures with a more substantial budget, blockchain-based security could pave a quick road to success. Known for its transparency, and the ability to store information within a number of encrypted networks, the decentralized ledger has become a revolutionary addition to a number of financial, and large-scale corporate firms.
In fact, 50% of all successful CEOs have revealed that blockchain-based technology has become critical to their cybersecurity infrastructure.
“The decentralized, consensus-driven, trustless nature of blockchain makes it naturally resilient to attack,” states business strategist and Forbes council member, Robert Napoli. “For those blockchain solutions utilizing proof of work validation methods (such as bitcoin), hackers have to gain control of a majority of nodes to compromise ledger transactions — something that is, by design, computationally expensive.”
Blockchain ensures that data is transferred both securely and transparently in a peer-to-peer B2B environment. Heavily dependent on numerous levels of authentication, business leaders that engage in a number of cross-border data and capital transfers can feel safe when exchanging sensitive information.
If you’re looking to seriously improve your venture’s cybersecurity in the long run, blockchain adoption is a must-have in any digital corporate strategy.
Develop A Recovery Plan
In order to be truly prepared for a cyber attack, small business owners should have a recovery plan in place.
After recent reports suggested that one in two small businesses could expect a data breach in the next two months, the odds of your security system being hacked are only increasing. In order to ensure that the impacts of a potential breach are reduced, entrepreneurs should continue to back up all data storage systems and identify a team member within the organisation that can safeguard physical copies of important information, company passwords and, most crucially, financial data.
With 60% of all startup data stored on laptops and mobile devices, it’s important that each and every file is accounted for in your backup solution. Tapping into the benefits of online security systems such as the cloud is key when prioritising user recovery.
As small business leaders move forward, cyber safety has never been so important. Despite extensive recovery strategies in place, it’s time for entrepreneurs to be forward-thinking when it comes to data security.